Employee Monitoring + Active Directory and SSO: Enterprise Deployment Guide
Employee monitoring software integrated with Active Directory and Single Sign-On gives IT administrators centralized access control, automatic user provisioning, and compliance-grade audit trails. This guide covers the complete deployment path: Azure AD SAML 2.0 configuration, SCIM provisioning, RBAC mapping, and the compliance benefits that justify the investment.
Why Does SSO Matter for Employee Monitoring Deployment?
Employee monitoring software integrated with Active Directory SSO is the standard deployment approach for enterprise organizations because it eliminates the credential fragmentation problem that makes large-scale software rollouts difficult. When employees authenticate to monitoring software using their existing corporate credentials, onboarding friction drops to zero, IT password management load decreases, and access control remains in the identity system the organization already governs.
The alternative, requiring employees to create and manage a separate username and password for monitoring software, creates predictable problems at scale. Password reset tickets for monitoring-specific credentials add IT support overhead. Employees who forget monitoring credentials may be flagged as absent from reporting dashboards even when they are working. And when an employee leaves the organization, a manually managed monitoring account may remain active unless IT has a disciplined offboarding checklist. SSO eliminates all three problems.
The Security Case for Centralized Identity
The 2024 Verizon Data Breach Investigations Report found that 74% of breaches involved the human element, with credential misuse as a primary attack vector. Centralized identity management through Active Directory reduces the attack surface by ensuring that a compromised employee account can be revoked from a single administrative location, cutting access to all SSO-connected applications simultaneously. For organizations managing sensitive employee data in monitoring software, this single-revocation capability is a meaningful security control.
The Compliance Case
SOX Section 404 (Sarbanes-Oxley internal controls), SOC 2 Type II (security and availability trust principles), and ISO 27001 (access control requirements) all require organizations to demonstrate that access to sensitive systems is granted on the principle of least privilege and revoked promptly when no longer needed. SSO integration with Active Directory provides the audit evidence for these requirements: every user's access to eMonitor is traceable to an AD account, every role assignment is justifiable by AD group membership, and offboarding is automatic and immediate rather than dependent on an IT checklist item.
How Does Azure AD SAML 2.0 Integration With eMonitor Work?
Azure Active Directory (now rebranded as Microsoft Entra ID) supports SAML 2.0 for enterprise application SSO. SAML 2.0 (Security Assertion Markup Language) is the authentication standard that allows an identity provider (Azure AD) to assert a user's identity to a service provider (eMonitor) without the user's password being transmitted to or stored by the service provider.
Step 1: Register eMonitor as an Enterprise Application in Azure AD
In the Azure AD admin portal (portal.azure.com), navigate to Enterprise Applications and select "New Application." Choose "Create your own application" and give it a name (for example, "eMonitor Employee Monitoring"). Select "Integrate any other application you find in the gallery" for a custom SAML integration. Azure AD will create a service principal for eMonitor in your tenant directory.
Step 2: Configure the SAML Assertions
In the eMonitor enterprise application settings in Azure AD, navigate to "Single Sign-On" and select SAML. You need four configuration values from eMonitor's enterprise support team: the Entity ID (the unique identifier for your eMonitor instance), the Reply URL (also called the Assertion Consumer Service URL), the Sign-on URL, and the Logout URL. Enter these values in the Azure AD SAML configuration form. The SAML assertion should be configured to send at minimum: user's email address (as the unique identifier), display name, and the AD groups the user belongs to (for RBAC mapping).
Step 3: Download and Upload the Federation Metadata
Azure AD generates a Federation Metadata XML file for your eMonitor enterprise application. Download this file from the Azure AD portal and upload it to eMonitor through the enterprise administration settings. The metadata contains the X.509 certificate Azure AD uses to sign SAML assertions, the SAML endpoint URLs, and the issuer identifier. Once eMonitor processes the metadata, the SSO configuration is technically complete on the eMonitor side.
Step 4: Assign Users and Groups
In the Azure AD enterprise application settings, navigate to "Users and groups" and assign the AD groups that should have access to eMonitor. This is the access control gate: only users who belong to an assigned group can authenticate to eMonitor via SSO. Users not assigned to the eMonitor application receive an access error when they attempt to log in, even if they have valid AD credentials. This prevents unauthorized access if an employee's email address is guessed or exposed.
Step 5: Test and Validate
Use Azure AD's "Test single sign-on" feature with a test user account before rolling out to the full organization. Verify that the user is redirected to the eMonitor login page when accessing the application URL, that Azure AD authenticates the user without a separate password prompt, and that the user's eMonitor role matches the expected mapping from their AD group membership. Test the full flow: login, session activity, logout, and the behavior when the AD account is disabled mid-session.
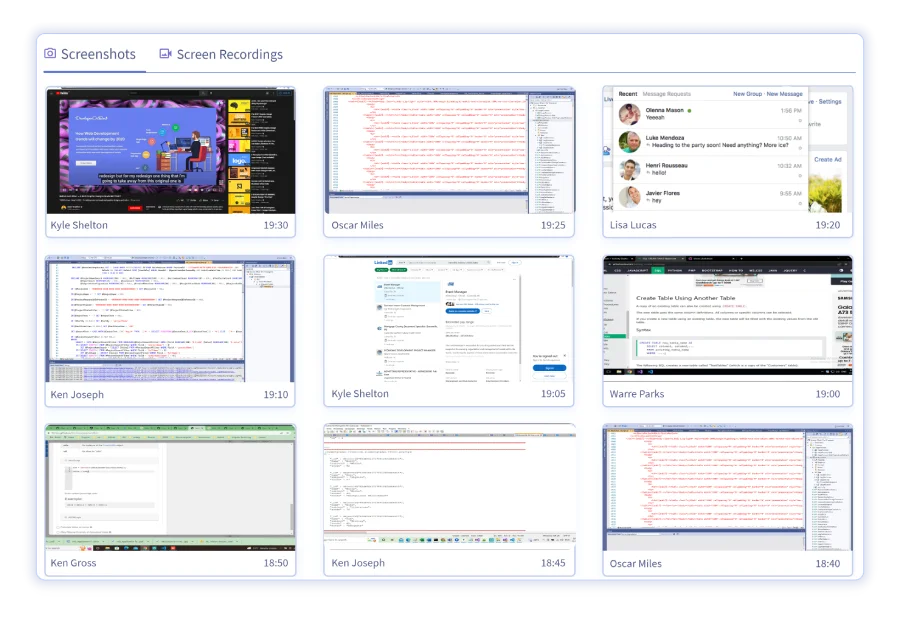
Team Productivity — This Week
Productive hours / day
Activity mix
▲ Deep-focus time up 19% after protecting daily focus blocks.
Illustrative eMonitor dashboard.
How Does On-Premises Active Directory Fit Into the Integration?
Organizations running on-premises Active Directory cannot connect directly to cloud-based SAML 2.0 applications because on-prem AD is a Kerberos/LDAP system, not a SAML identity provider. The standard integration path uses Azure AD Connect, Microsoft's hybrid identity synchronization tool, to replicate on-prem AD user accounts and group memberships to Azure AD in the cloud.
Azure AD Connect Synchronization
Azure AD Connect runs as a service on a Windows Server in the on-premises environment and synchronizes user accounts, group memberships, and password hashes (or authentication flows, for pass-through authentication deployments) to Azure AD on a configurable schedule, typically every 30 minutes. Once synchronization is established, user accounts created in on-prem AD appear in Azure AD and can be assigned to enterprise applications including eMonitor. The net result: IT administrators manage users in on-prem AD as they always have, and Azure AD Connect keeps the cloud identity in sync automatically.
Password Synchronization vs Pass-Through Authentication
Azure AD Connect supports two primary authentication modes. Password Hash Synchronization copies hashed passwords from on-prem AD to Azure AD, enabling cloud authentication even when on-prem infrastructure is unavailable. Pass-Through Authentication forwards authentication requests to an on-prem agent, which validates credentials against local AD without storing passwords in the cloud. For most monitoring deployments, Password Hash Synchronization is simpler and more resilient. Pass-Through Authentication is preferred by organizations with strict data residency requirements that prohibit password hash storage in Azure.
Considerations for Hybrid Environments
Organizations running Active Directory Federation Services (AD FS) on-premises can also integrate eMonitor via SAML 2.0 through AD FS as the identity provider rather than Azure AD directly. This path is less common in 2026 as most organizations have migrated to or are migrating to Azure AD, but it remains valid for environments where AD FS is an established part of the identity architecture. The SAML configuration steps are structurally similar; the key difference is that the Federation Metadata XML comes from the AD FS server rather than Azure AD.
What Is SCIM Provisioning and How Does It Automate User Management?
SCIM (System for Cross-domain Identity Management) is an open standard (RFC 7642-7644) that enables identity providers to automatically create, update, and delete user accounts in connected SaaS applications. For employee monitoring deployments, SCIM provisioning means new employees get eMonitor access automatically when they are added to the right AD group, and departing employees lose access the moment their AD account is disabled.
Configuring SCIM Provisioning in Azure AD
In the eMonitor enterprise application in Azure AD, navigate to the "Provisioning" section and set the provisioning mode to "Automatic." You need two values from eMonitor: the SCIM endpoint URL (the API endpoint Azure AD will write provisioning events to) and a bearer token (for authenticating Azure AD's provisioning requests to eMonitor). Enter these values in the Azure AD provisioning configuration. Azure AD will send a test provisioning request to confirm connectivity before activating the provisioning cycle.
Configure the attribute mappings to ensure that the correct user fields in Azure AD populate the corresponding fields in eMonitor: display name, email address (the unique identifier), department, job title, and manager. The department and job title fields are particularly useful for eMonitor deployments because they allow activity data to be automatically segmented by department without manual configuration of reporting groups.
Automatic Offboarding: The Security Benefit
When an employee's Active Directory account is disabled (standard offboarding procedure in most organizations), Azure AD's SCIM provisioning engine sends a deprovisioning request to eMonitor within the next provisioning cycle (typically within 40 minutes). The eMonitor account is disabled, the user's session is terminated if active, and the account is flagged as inactive in the eMonitor audit log. This automatic offboarding is significantly more reliable than manual deprovisioning checklists, which are frequently missed or delayed when HR and IT are coordinating across a departing employee's last day.
Just-in-Time Provisioning vs SCIM: Which to Use?
Just-in-time (JIT) provisioning creates a user account in eMonitor when the user authenticates via SSO for the first time. This approach is simpler than full SCIM provisioning but has two limitations: the user must log in at least once before their account exists in eMonitor (meaning they will not appear in any reports on their first day if they have not yet logged in), and offboarding is not automatic (only future SSO attempts are blocked; the eMonitor account record persists). SCIM provisioning solves both limitations and is recommended for organizations where HR reporting accuracy from day one and clean offboarding are priorities.
How Does RBAC Mapping From AD Groups to eMonitor Roles Work?
eMonitor's role-based access control system defines what each user can see and do within the monitoring platform. The four primary roles are: Administrator (full access to all data, all settings, and all employees), Manager (access to monitoring data for their direct reports and team), HR Viewer (access to aggregate reports and attrition analytics, no individual detailed monitoring data), and Employee (access to their own data only).
Mapping AD Groups to eMonitor Roles
The SAML assertion from Azure AD includes the user's AD group memberships as claims (the groups the user belongs to in AD). eMonitor's SAML configuration maps these group claims to eMonitor roles. A typical mapping configuration looks like this:
- AD group eMonitor-Administrators maps to eMonitor Administrator role
- AD group eMonitor-Managers maps to eMonitor Manager role
- AD group eMonitor-HR maps to eMonitor HR Viewer role
- All other users with eMonitor access default to the Employee role
When a manager joins the organization or is promoted, IT adds them to the eMonitor-Managers AD group. On their next login, the SAML assertion includes the new group membership and eMonitor updates their role automatically. No manual role assignment is needed inside eMonitor, and no separate IT ticket is required beyond the standard AD group membership update.
Departmental Scoping Through AD Groups
For organizations with multiple business units that should not have cross-visibility, eMonitor supports departmental scoping combined with AD group assignments. A Finance department manager should see monitoring data for Finance employees but not Engineering employees. This is implemented by creating department-specific AD groups (for example, eMonitor-Managers-Finance and eMonitor-Managers-Engineering) and mapping them to Manager roles scoped to the corresponding department in eMonitor. IT maintains the group memberships; eMonitor enforces the visibility boundaries.
Multi-Tenant Deployments: How Do Enterprises With Multiple AD Tenants Handle Monitoring?
Large enterprises and holding companies frequently operate multiple Azure AD tenants: one per subsidiary, region, or acquired company. Multi-tenant eMonitor deployments require a separate enterprise application registration in each Azure AD tenant, with SAML and SCIM configured independently for each. All tenant data flows into a unified eMonitor account, with tenant-specific organizational units maintaining data separation for reporting and compliance purposes.
Cross-Tenant Visibility for Group Leadership
A common requirement in multi-tenant deployments is that corporate group administrators need visibility across all subsidiaries, while subsidiary-level administrators see only their own tenant's data. This is configured through eMonitor's organizational hierarchy: subsidiary tenants are nested under a parent organization, and the group administrator account (authenticated against the parent tenant's Azure AD) is granted parent-level Administrator access that spans all nested organizations.
Compliance in Multi-Tenant Environments
Multi-tenant monitoring deployments add complexity to GDPR and other privacy law compliance because each subsidiary may operate in a different jurisdiction with different monitoring disclosure requirements. The practical approach is to configure tenant-specific monitoring policies in eMonitor that reflect the disclosure and consent mechanisms active in each subsidiary's jurisdiction, while maintaining unified reporting at the group level. Legal review of the monitoring disclosure policies across all tenants is recommended before activating cross-tenant visibility for group-level users.
Deploy eMonitor Across Your Enterprise With SSO in Days, Not Weeks
eMonitor supports Azure AD SAML 2.0 and SCIM provisioning for enterprise deployments. Trusted by 1,000+ companies worldwide. Book a demo to see the enterprise deployment flow.
Troubleshooting Common SSO Integration Issues
SSO integrations for employee monitoring software share a predictable set of configuration errors. Most login failures during initial deployment trace to one of the following causes.
SAML Assertion Validation Failures
The most common cause of SAML login failures is a clock skew between the Azure AD server and the eMonitor application server. SAML assertions include a validity window (typically 5 minutes). If the two systems' clocks differ by more than this window, the assertion is rejected as expired or not-yet-valid. The fix is to ensure both systems are synchronized to NTP time sources. In Azure AD, clock synchronization is managed by Microsoft. On the eMonitor side, ensure the server or container running eMonitor is synchronized to a reliable NTP source.
A second common cause is a mismatch between the Entity ID configured in Azure AD and the Entity ID eMonitor expects. Entity IDs are case-sensitive strings; a trailing slash difference or case mismatch between https://app.emonitor.io/saml and https://app.emonitor.io/saml/ causes the assertion to fail. Verify the Entity ID from eMonitor's SAML metadata against what is configured in Azure AD exactly, character for character.
Group Claims Not Appearing in SAML Assertions
If RBAC mapping from AD groups is not working, the most likely cause is that group claims are not being sent in the SAML assertion. In Azure AD, group claims must be explicitly enabled in the enterprise application's SAML token attributes configuration. Navigate to the enterprise application, then "Single Sign-On," then "Attributes and Claims," and add a group claim that sends the user's group memberships. By default, Azure AD sends all group memberships; for users who belong to more than 150 groups, Azure AD sends only group memberships for groups assigned to the enterprise application (this is the "overage claim" limitation).
SCIM Provisioning Delays
Azure AD's SCIM provisioning cycle runs every 20-40 minutes by default. After making changes to AD group membership (adding a new user or changing a user's department), those changes appear in eMonitor within the next provisioning cycle. For immediate propagation, IT administrators can trigger a manual provisioning cycle from the Azure AD portal by navigating to the enterprise application's Provisioning settings and selecting "Provision on demand," entering the specific user to provision or deprovision immediately.
Frequently Asked Questions: Employee Monitoring Active Directory SSO
What is employee monitoring Active Directory SSO integration?
Employee monitoring Active Directory SSO integration connects workforce monitoring software to an organization's identity provider (typically Azure AD or on-premises Active Directory) so that employees authenticate to the monitoring platform using their existing corporate credentials. IT administrators manage access through AD group membership, and monitoring access is automatically revoked when an employee's AD account is disabled.
Why use SSO for employee monitoring deployment?
SSO eliminates the need for employees to create and manage a separate password for the monitoring platform. This reduces friction at onboarding, simplifies the IT support burden (no monitoring-specific password reset tickets), and ensures that access control remains centralized in the organization's existing identity management system rather than fragmented across SaaS tools.
Does eMonitor support SAML 2.0 with Azure Active Directory?
eMonitor supports SAML 2.0 integration with Azure Active Directory (now Microsoft Entra ID). The integration allows IT to register eMonitor as an enterprise application in the Azure AD portal, configure SAML assertions, and enable SSO so employees authenticate with their Microsoft 365 credentials. Contact eMonitor's enterprise support team for the SAML metadata and configuration checklist.
What is SCIM provisioning and why does it matter for monitoring?
SCIM (System for Cross-domain Identity Management) is an open standard for automating user provisioning between identity providers and SaaS applications. With SCIM provisioning, new employees added to Active Directory are automatically created in eMonitor, and employees who leave the organization are automatically deprovisioned. This eliminates the risk of orphaned monitoring accounts for former employees.
How does SSO help with SOX and SOC 2 compliance?
SOX Section 404 and SOC 2 Type II both require demonstrable controls over who has access to systems that process or store sensitive data. SSO integration means access to employee monitoring software is governed by the same centralized identity management controls auditors examine for other enterprise systems. This simplifies the audit evidence package and demonstrates consistent access governance rather than tool-by-tool credential management.
Can eMonitor roles be mapped from Active Directory groups?
Yes. eMonitor's RBAC system supports mapping from Azure AD group membership to eMonitor permission levels. An AD group called 'Monitoring-Admins' can be mapped to the eMonitor Administrator role, 'Monitoring-Managers' to the Manager role, and 'Monitoring-HR' to the HR Viewer role. Group membership changes in AD propagate to eMonitor permissions without manual intervention.
What happens to eMonitor access when an employee leaves?
With SSO and SCIM provisioning configured, disabling an employee's Active Directory account automatically revokes their eMonitor access. For organizations using just SSO without SCIM, disabling the AD account prevents future logins but does not remove the eMonitor user record. SCIM provisioning is recommended for organizations where offboarding speed is a security or compliance requirement.
How does just-in-time provisioning work for employee monitoring?
Just-in-time (JIT) provisioning creates an eMonitor user account automatically when a new employee authenticates through SSO for the first time. The employee's AD attributes (name, email, department, manager) populate the eMonitor profile without manual data entry by IT. Combined with AD group-to-role mapping, new employees receive the correct eMonitor permission level on their first login without any IT intervention.
What is the difference between on-premises Active Directory and Azure AD for monitoring?
On-premises Active Directory requires Azure AD Connect to synchronize user accounts to Azure AD before SSO integration with cloud SaaS applications like eMonitor is possible. Azure AD (now Microsoft Entra ID) is Microsoft's cloud identity platform and connects directly to SAML 2.0 SSO applications. Organizations with hybrid environments typically run Azure AD Connect to maintain a single identity source that covers both on-prem and cloud-based tools.
Can monitoring access be scoped per department through AD?
Yes. eMonitor's RBAC model supports departmental scoping: a Finance manager can see monitoring data only for employees in the Finance department, not the Engineering department. This scope is maintained through AD group assignments: employees belong to department groups, managers are assigned view rights over their department group, and cross-department visibility requires explicit Administrator-level access. The entire permission model is maintained through AD without requiring manual configuration in eMonitor for each new manager.
Sources
- Verizon 2024 Data Breach Investigations Report — credential misuse statistics
- Sarbanes-Oxley Act Section 404 — internal controls over financial reporting
- AICPA SOC 2 Trust Service Criteria (2017 with 2022 revisions) — access control requirements
- IETF RFC 7642-7644 — SCIM 2.0 standard specification
- Microsoft Entra ID (Azure AD) documentation — SAML 2.0 and SCIM provisioning technical reference
Related Blogs
Ready to Deploy eMonitor With Your Enterprise Identity Stack?
eMonitor supports Azure AD SAML 2.0, SCIM provisioning, and RBAC from AD groups. Trusted by 1,000+ companies worldwide. Our enterprise team handles the SSO configuration alongside your IT team.

